作者
標題 [臉書] 峰言峰語 20190425
時間 Thu Apr 25 21:24:07 2019
時間 Thu Apr 25 21:24:07 2019
臉書卦點說明:
說明華人社會裡,父輩資源才是成功的關鍵;
但是為什麼都避口不談呢?
知道又能怎麼樣?
臉書連結:
https://www.facebook.com/mapleduh0703/
FB內容:
【競爭的本質:代際競爭】
#重點1
#華人社會,父輩資源才是成功的關鍵
從小到大,不論是學校、媒體、社會……所傳達的競爭力觀點,多將成功歸因為個人能力,但這可能不符合我們在生活所見。然而,若能將『個人競爭』轉化為『代際競爭』,那將有助我們更正確地認識這個世界。
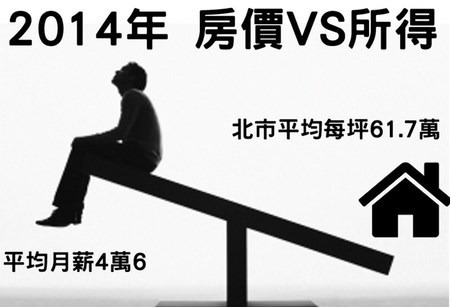
『代際競爭』指的是,個人的成功除了本身的能力外,更重要的,還有父祖輩所帶來的優勢,簡言之,代際競爭 = 父輩資源 + 個人能力。然而,與傳統觀念大相逕庭的是,在『父輩資源』與『個人能力』間,我認為在華人社會中,父輩資源更能決定你的未來。
正如同站在巨人的肩膀你能看得更遠,而有個資源豐沛的家庭,你也能比其它人更易成功。我在《創意重要,錢更重要》曾說,過了四十歲,你會發現許多有能力的朋友依舊失意,而發展最好的,往往是資源豐富的富二代。當然,我並非指個人能力不重要,而是說在這二者中,父輩資源才是決定性因素。
了解這點後,我們才有辦法更全面地觀察他人的成功軌跡,也只有正確地理解事實時,才能真正學到東西。相反地,如果沒有透過正確的觀察,而只是片面地相信富二代所吹捧的成功學,你會發現透過同樣的操作模式,通常只會賠光所有。
《創意重要,錢更重要》
mapleduh.pixnet.net/blog/post/45545197
#重點2
#為何這世界避口不談父輩資源?
首先,個人競爭力的觀點,一開始是由美國而來,在美國,因制度良善與科技先進,個人能力確實是成功的主要因素,以 forbes 的前四百大富豪來看,白手起家者高達七成。然而,台灣並沒有類似美國的環境與制度,除了1970年代因時代機運造就了一批白手起家者,其它時候,你會發現99%的富豪皆是克紹箕裘。
其二,對魯蛇家庭,他必須強調個人能力。這主要是魯蛇家庭多半沒有代際競爭的觀念,不過就算知道了,家長也不能強調父輩資源的重要性,因為如此非但無助於教育,而且只會讓小孩對未來失去希望。
其三,對富有家庭,他必須強調個人能力。富二代已不欠錢,他所欠的是一種肯定,試想,如果富二代強調父輩資源才是他們成功的主因,那不就等於直接否定自己?
其四,強調個人能力是種政治正確。不可否認地,將成功歸因於個人能力確實能激勵人們奮發向上,對社會形成良好風氣,試想,若一個社會都感覺要靠爸才能更好時,這社會還會有希望嗎?
其五,對地主民代,他必須強調個人能力。因為父輩資源要發揮優勢,很大一部份必須透過制度(土地制度、稅制、貨幣……)來向廣大人民來掠奪。如果強調父輩資源才是成功的主因,那會將人民的眼光轉移到制度改革,這對地主民代會是很大的傷害。
以上五點,有惡意,也有善意,卻共譜了一個普世的驚天謊言,讓我們相信『個人能力』才是成功的主因,即使它與我們所觀察到的相去甚遠。
談完父輩資源,再回頭談個人能力。這其中有個重要的思考,那就是:個人能力是父輩資源的延伸嗎?個人以為,不完全是,但有很大一部份是。
事實上,現今很多的菁英,從小就來自優渥的家庭,這樣的家庭所給予的,絕非只有物質上的幫助,這還包括了他們性格上的訓練,例如勤儉、紀律、堅韌……,甚至在出社會後,都還有父輩人脈的舖墊,而這種『非物質』的助力,很多時候它的重要性甚至遠超過金錢。
個人確實有資質之分,但我們也必須承認,父母資源在個人成長中的重要助力,若能認清這點,你將會發現在上述『代際競爭 = 父輩資源 + 個人能力』的公式中,父輩資源的比重再次被拉高,而個人能力的重要性則再次降低。
#重點3
#轉化為『代際競爭』觀點有什麼好處?
1、對事物能有更正確的認識。如前所述,了解到競爭的本質其實是『代際競爭』後,你才有辦法更全面地思考,唯有如此時,才能真正學到東西。
2、離成功更近。承上,因為更能正確地掌握成功的全貌,你才會由自己所掌握的資源來思考成功的軌跡,這樣的思考,才能放大成功的機率。
3、對人生更為豁達。當你看到別人的成功時,不會自怨自艾不如人,同理,當你看到他人失意時,也能理解或許只是自己比較幸運罷了。當你對人生會更為豁達時,也就更接近人生的真諦:快樂。
4、衡量成功的標準更健康。了解競爭的本質是『代際競爭』後,你會理解每個人的起步資源不同,與他人比較也就成了沒有意義的事,所以你最後衡量成功會是一種更健康的觀點,那就是只會著重於自己的努力,而非與他人相較,一如我在《重點在於,你能將資源放大到多少?》所說。
《重點在於,你能將資源放大到多少?》
mapleduh.pixnet.net/blog/post/44587987
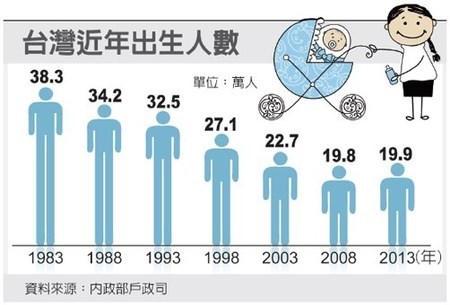
5、你會更重視下一代的教育。你會知道,你小孩將來的成就,你的責任很大,你會了解到代際競爭就如同大隊接力一樣:你父親傳給你他最盡力的一棒,而你也會傳給你小孩最盡力的一棒,不一定是最好的,但絕對是最盡力的。
《創意重要,錢更重要》
mapleduh.pixnet.net/blog/post/45545197
--
噓 billchen****:怪就怪自己趴數不夠 要出社會賺錢 想要賺錢 被凹也是 10/26 20:07
→ billchen****:剛好而已 講的那麼憤慨 有種自己出來當老闆啊 10/26 20:07
→ billchen****:員工本來就是不能疼的 對員工好 員工知道甜頭之後 10/26 20:08
→ billchen****:只會越來越難管 到時後苦的倒楣的還是老闆 10/26 20:08
→ billchen****:所以不要只會怪老闆 爭氣點吧 10/26 20:09
--
※ 發信站: 批踢踢實業坊(ptt.cc), 來自: 61.31.131.137
※ 文章代碼(AID): #1SmRJw-9 (Gossiping)
※ 文章網址: https://www.ptt.cc/bbs/Gossiping/M.1556198650.A.F89.html
噓 : 你以為外國家世就不重要嗎1F 04/25 21:26
噓 : 父權遺毒啦2F 04/25 21:27
→ : 靠爸兩個字 講那麼複雜3F 04/25 21:28
→ : 外國不是早就調查過了 有錢的家族 過了十幾代 絕大部
→ : 分一樣是有錢人
→ : 外國不是早就調查過了 有錢的家族 過了十幾代 絕大部
→ : 分一樣是有錢人
推 : 真相 說的很好 而且有積極意義6F 04/25 21:36
--
※ 看板: Gossiping 文章推薦值: 0 目前人氣: 1 累積人氣: 340